Why Sharetru?
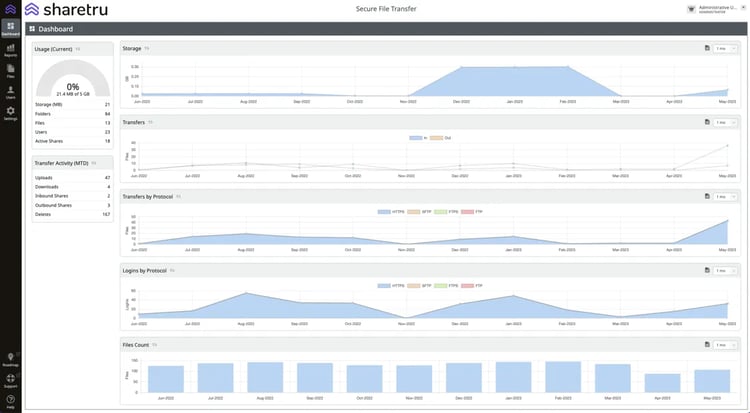
Platform
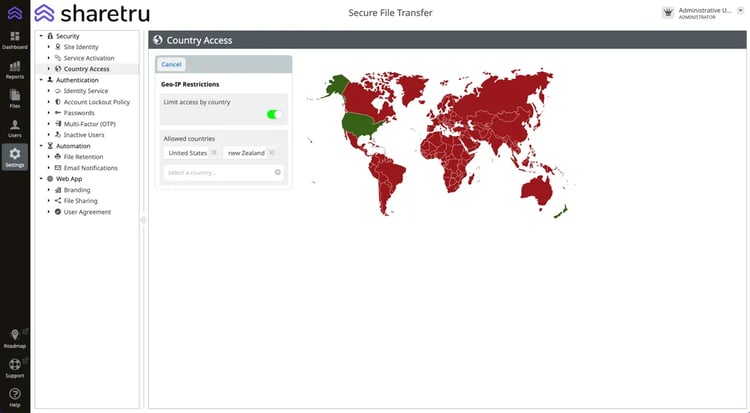
Features
Compliance