Cybersecurity threats exist all around us, no matter what industries we may work in. The organizations that emphasize computer security best practices are the ones that will succeed at preventing threats from becoming realities.
Training in computer security isn’t always handled properly, though. To ensure that your organization is staying safe from cybersecurity threats, here’s a look at computer security best practices for fighting internal and external threats, as well as best practices for keeping data safe from former employees.
Protect Data from Outside Threats
Your employees won’t always know instinctively how to protect sensitive files and information. That’s why you need to create policies and procedures that make it easy for all team members to act responsibly in regards to your sensitive data. Here’s a look at 8 best practices for computer security and protecting your data from outside threats.
1. Elevate & Update Passwords
Because of an increased emphasis on cybersecurity, we’ve come a long way since the days when people used “password” or “123456” as their passwords. Your organization should always require complex passwords. What makes a password complex? As we wrote about in a post about computer security training tips, strong passwords have:
- Both upper and lowercase letters.
- Strings of unrelated numbers.
- At least one symbol.
- A minimum of 8 characters.
- Non-dictionary words.
- Never before been used on another system (each password is unique)
Don’t stop at complex passwords. You should also force all team members to update their passwords on a regular basis. While this may be frustrating for employees, it’s a key tactic for computer security. Their frustration can be overcome with proper training regarding the threats that face your organization. Updates every 60 to 90 days create a good, secure cadence.
2. Use Only Secure Connections
Force your employees to always use secure connections. This is easy when your team members are working in your own office. It’s more difficult when employees are working remotely or in public spaces using public wi-fi.
Check out our Data Security Training Guide for more information on secure connections and generally managing cybersecurity risk related to your employees.
3. Avoid USBs
Removable storage like USBs is often thought to be a strong alternative for securely sharing files and data. But nothing could be further from the truth.
USBs often get lost, and you never know who will end up with your files and data if your USB does go missing. The best way to prevent such a situation is eliminating the use of removable storage altogether.
4. Beware BYOD
The bring-your-own-device concept is popular for several reasons. Employees know their own devices better than yours. It’s affordable for organizations. And it generally streamlines the onboarding process for new team members. But approach BYOD with extreme caution.
Your employees’ devices (which are not administered by a professional IT team) are going to be less secure than your own devices. This leaves them more vulnerable to hackers.
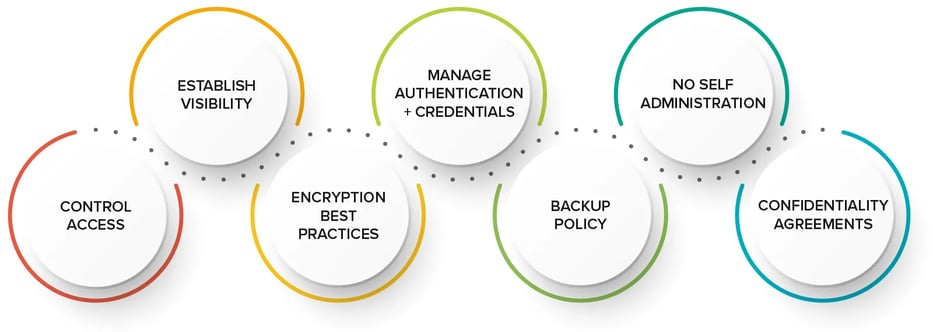
8 WAYS TO PROTECT DATA FROM OUTSIDE THREATS
5. Think Before You Click
Teach employees how to think before they click on links. They can see the destination URL by hovering over a hyperlink. If the link looks suspicious or fraudulent, there’s no reason to risk clicking on it. Your employees should also look for typos, misspelled names, uncommon greetings for your region, etc.
Hackers are getting savvier with each passing day about creating emails and landing pages meant to look legitimate. Even though emails and landing pages look legit, they may not be. It’s important for your team members to be able to discern between what’s real and what is not. Hovering over and inspecting links before clicking is one of the best approaches.
Finally, make sure your team members are aware of social engineering tactics used by hackers. These tactics could include acting like employees to gain access to systems, developing relationships with employees, walking by desks looking for credentials on sticky notes, etc.
6. Use Two-Factor Authentication
We wrote about data security tips more than 5 years ago, and the points we made then still hold true in 2022 and beyond. One of the tips we shared was this: Emphasize and use two-factor authentication. This is one of the best ways to defeat social engineering and phishing attacks that can give hackers access to your organization’s systems. If a hacker gains access to a system because of a link or a misplaced password and username, the second of the two factors can stop them dead in their tracks.
7. Keep Machines & Applications Updated
Always keep your organization’s machines and software updated to the latest security releases. This is especially important for remote workers. As noted above, hackers and the technologies they use are becoming more advanced with each passing day. Regular computer and application updates can make for a great defense against hackers.
8. Promote Secure File Sharing
Just as we’re (hopefully) all way past using “password” as a password, we should also be past using email to send sensitive files and information. Email does not offer the level of security your most sensitive files and information demand. Instead, use a secure file sharing solution, and create strict guidelines for information storage, sharing and saving.
Protect Data From Former Employees
You’ve likely heard about the so-called Great Resignation, and your organization may even be feeling the effects of it. As turnover increases, you need to secure your data from former employees.
Your former team members may inadvertently remove sensitive proprietary information if not secured. In some cases, former team members may not realize that removing sensitive files and information is wrong. And, in rare cases, some former team members may actually want to do harm to your business after they depart.
No matter the reason a former employee leaves with sensitive files and information, you can prevent these situations from happening altogether by following these 7 computer security best practices. (And, you’ll notice, these tactics should be implemented before anyone leaves your organization — not after.)
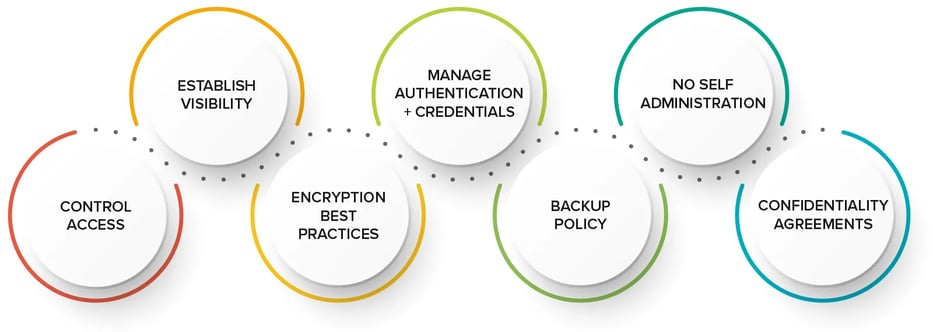
7 WAYS TO PROTECT DATA FROM FORMER EMPLOYEES
.webp?width=960&height=343&name=protect-data-former-employees%20(1).webp)
1. Control Access to Data
Not everyone in your organization needs access to sensitive files and data. If they do need access to some sensitive information, there’s a low likelihood they need access to ALL sensitive information. You should always limit access to data among your team members. That way, you don’t have to worry about your most sensitive information being at risk each time someone leaves your organization.
2. Establish Visibility Across Your Sensitive Data
Do you know who is accessing your sensitive data? It’s important to have in place a system that tracks who is accessing sensitive data, how they’re accessing it, when they’re accessing it, etc. Your logs should be accessible to only administrators, which is key to creating a strong internal security posture and meeting external compliance requirements.
It’s also important to have safeguards against the changing of these logs to prevent bad actors from making edits to cover their steps. With proper safeguards, you’ll always have accurate logs of who accessed your sensitive files and when.
3. Follow Data Encryption Best Practices
Your organization should be familiar with and follow encryption best practices. That includes encrypting files both at-rest and in-transit.
4. Carefully Manage Credentials & Authentication
You want to limit access to sensitive files and data to only authorized users, as mentioned above. The best ways to enforce access controls are through careful credentialing and authentication processes.
Administrators should be able to easily add and remove a user’s credentials from the system. Ease of removal helps prevent former employees from accessing sensitive files and information. This process can be automated in many cases, including auto-suspensions when contracts expire or after a certain number of days without use.
5. Enact a Backup Policy
Many organizations allow for personally managed tools to be used among their team members. IT teams are unable to backup files and data stored by these personally managed tools because they’re not administered by the organization.
You should have in place a strong backup policy so that your organization is able to backup as close to 100% of all files and data as possible. The personally managed tools allow for any team member to save proprietary files and data, and then to retain access even after they leave your company. There’s no stopping this completely, but giving them a company-provided area to store files helps an organization overcome much of this challenge.
6. No Self-Administration
Employees should not be their own administrators. If a team member is the administrator of his or her laptop, for example, it’s easy to download tools for storing and sharing sensitive files and information in places beyond the IT team’s influence and control.
7. Use Confidentiality Agreements
If you store, share or otherwise handle sensitive files and information, it’s essential you insert confidentiality agreements into your employment contracts. These agreements give you something enforceable to work from if and when a team member leaves your organization with sensitive files or information.
Get Support for Your Data Security
As you look through the data and computer security training best practices listed above, you’ll discover that a platform like Sharetru can greatly enhance your ability to keep secure data, files and information safe and secure.
When you choose to work with Sharetru, you instantly get at-rest and in-transit encryption for your sensitive files, you get access controls and logs for your sensitive files, and you enjoy automated backups of all your sensitive files. Partnering with a solution like Sharetru helps your organization operate computers and handle sensitive data securely so that your team can focus on other high-value tasks.
Contact us for a brief demo and more information about how Sharetru can help you follow data and computer security best practices.


.webp?width=960&height=343&name=protect-data-former-employees%20(1).webp)
